New Enhancements to Verified ANALYTICS
Verified ANALYTICS analyses the data already collected within your Google Analytics reports. Rather than relying on assumptions or configuration reviews, it inspects actual values across key dimensions where PII is most likely to appear.
Our AI detection technology, powered by Google, scans for potential personal data in your Google Analytics account and allows you to monitor this. These latest improvements boost both the accuracy and efficiency of this process.
What’s New – Four Key Improvements to PII Detection:
1. Immediate Insight from the Project Overview
You can now see, at a glance, whether the most recent audit identified potential PII—directly from the project listing view. This provides an immediate signal for teams prioritising privacy risk, enabling faster triage without needing to open individual audit reports.
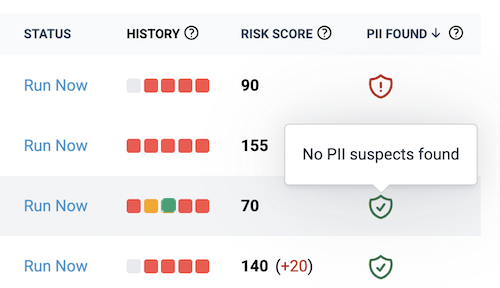
At a glance notice of suspected PII values.
2. Smarter Data Pre-processing at Scale
To ensure efficient analysis of large datasets, audits intelligently sample up to 30,000 rows. Where volumes exceed this, sampling is distributed across high-, medium-, and low-frequency data. This approach improves detection coverage by capturing both dominant patterns and less frequent edge cases—where PII often appears.
You now have greater control over what is analysed. For example, query parameters used for internal search (e.g. ?q=) can be excluded from checks where they legitimately contain contact details, such as staff email addresses. The remainder of the URL continues to be assessed.
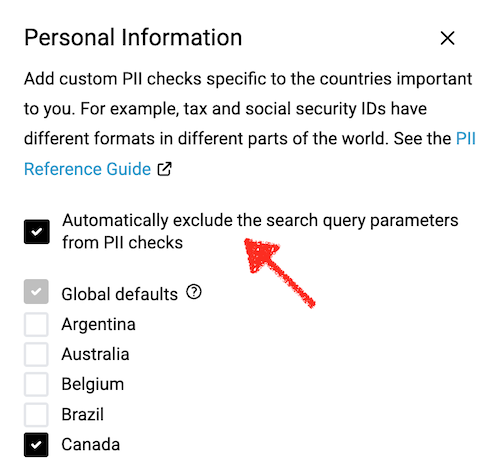
You can now exclude search terms from the PII checks.
3. Expanded and Optimised Detection Coverage
PII rarely appears in obvious formats. While email addresses are a common example, they represent only a fraction of real-world leakage.
Detection has been refined and expanded across key analytics fields, including:
- Page URLs
- Page Referrers
- Campaign parameters
- Event data
- Transaction fields
- Custom dimensions
These are common sources of unintended data exposure, particularly where user input or dynamic identifiers are captured.
4. More Flexible Bypass Management
While highly effective, no automated system is completely accurate. To manage false positives, you can maintain a Bypass List—approving known, acceptable values to be excluded from future audits.
You can now review and reverse previous decisions, including bypass items created in earlier audits, giving you full control and auditability over time.
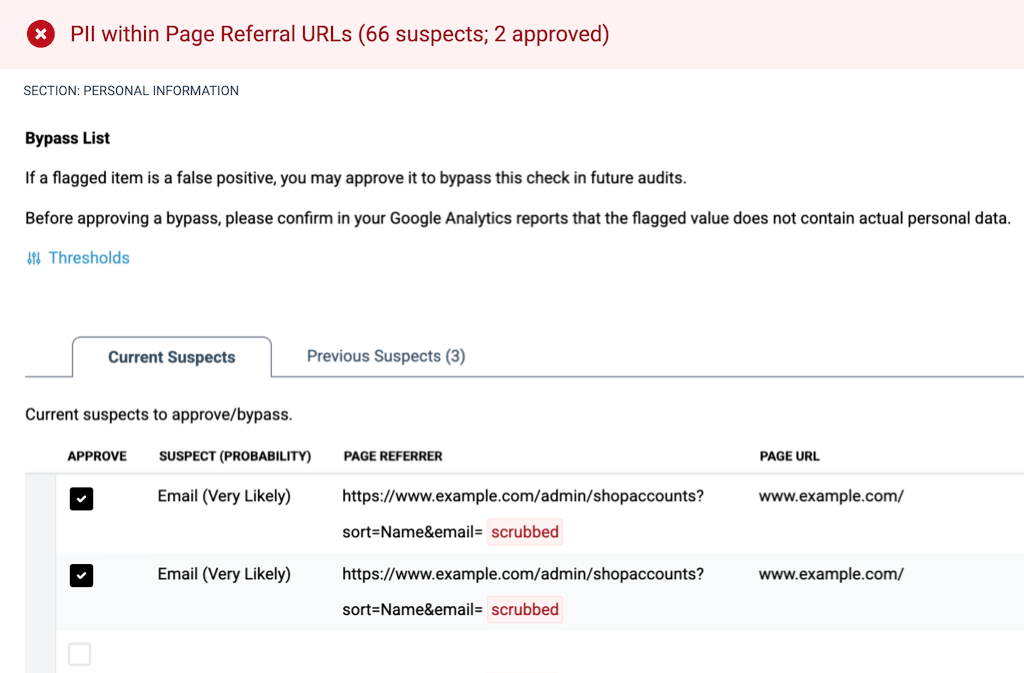
The Bypass list allows you to manage false positives. Suspected PII values are never stored in their original form.
Built for Ongoing Privacy Assurance
These updates reflect a continued focus on analysing real data, not assumptions—helping you identify where personal data may actually be flowing through your analytics setup.
For existing users, this means faster insight, broader detection coverage, and more control.
For new users, it highlights a scalable, data-driven approach to monitoring analytics environments for potential privacy risk.
Log in and explore the new experience.
As always, your feedback is essential — we are always learning. Let us know what works, what could be better, and what you’d like to see next. You can reach me directly at hello—{@}—verified-data.com.